ABSTRACT
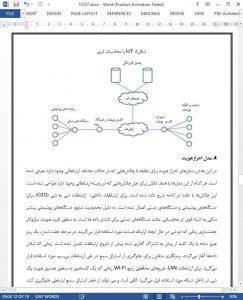
IoT (Internet of Things) diversifies the future Internet, and has drawn much attention. As more and more gadgets (i.e. Things) connected to the Internet, the huge amount of data exchanged has reached an unprecedented level. As sensitive and private information exchanged between things, privacy becomes a major concern. Among many important issues, scalability, transparency, and reliability are considered as new challenges that differentiate IoT from the conventional Internet. In this paper, we enumerate the IoT communication scenarios and investigate the threats to the large-scale, unreliable, pervasive computing environment. To cope with these new challenges, the conventional security architecture will be revisited. In particular, various authentication schemes will be evaluated to ensure the confidentiality and integrity of the exchanged data.
1. INTRODUCTION
Internet of Thing (IoT) is a self-configuring and adaptive complex network that interconnects uniquely identifiable “Things” to the Internet through the use of interoperable communication protocols. The “Things”, sometimes referred to as devices or objects interchangeably, have sensing/actuation and potential programmability capability. Information about the “Thing” can be collected from anywhere, at anytime, by anything. IoT attracts much attention as the economic prosperity generated by the technology [1]. One of the economic opportunities is based on the data that the “Things” on the Internet shared. The shared data is processed into information as the input for other “Things” or as reports for human to read [2]. Given the data that has been shared over a network medium, namely the Internet, it is important to protect the shared data as it may contain sensitive and private information [3]. With the growth of the technology on Big Data, the threat is severer since the attacker may obtain private information through the raw data leaked by the compromised objects. Thus, privacy preservation becomes a critical issue to address.
5. CONCLUSION
In this paper, emerging security threats and countermeasures in IoT are investigated. In particular, challenges to sensitive and private information exchanged between travelling objects and objects at home/organization are evaluated. Naming, identity management, and authentication of IoT objects are the key issues for secure communication and data retrieval. Based on various communication scenarios in IoT, we enumerated a few potential authentication schemes that are applicable. Hopefully this attempt can motivate more future work to cope with security concerns in the deployment of IoT.